Core Conclusion
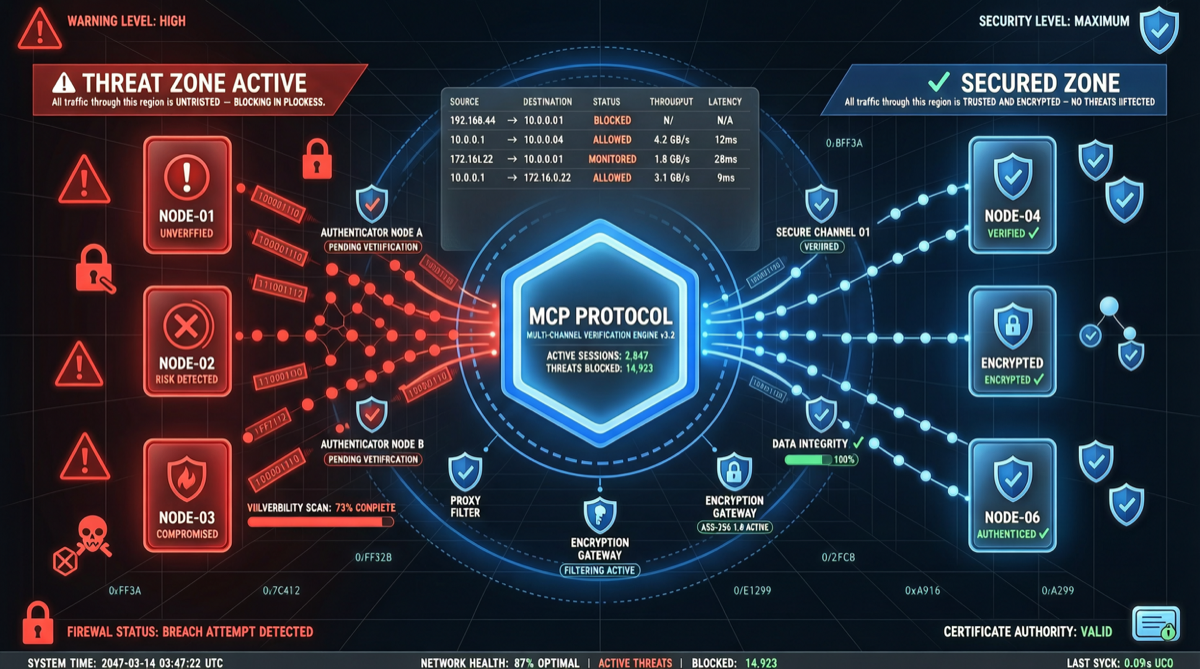
MCP (Model Context Protocol) is experiencing a critical leap from “open-source protocol” to “enterprise infrastructure.” Google Cloud launched 50+ managed MCP servers in one go, covering nearly all core cloud services; simultaneously, security experts warn that unverified MCP servers could become data leakage channels in Agent workflows.
Key contradiction: MCP enables AI Agents to seamlessly connect to external tools, but “connection” itself brings trust questions—how does your Agent know the MCP server it connects to is safe?
MCP Server Ecosystem Map
Google Cloud Managed MCP Servers (April 2026)
| Category | Covered Services | Count |
|---|---|---|
| Database | Cloud SQL, BigQuery, Firestore, Spanner | 12+ |
| AI/ML | Vertex AI, Gemini API, AI Platform | 8+ |
| Operations | Cloud Monitoring, Logging, Cloud Run | 10+ |
| Security | IAM, Secret Manager, Security Command Center | 6+ |
| Docs/Office | Google Workspace, Docs, Sheets | 8+ |
| Other | Pub/Sub, Cloud Storage, API Gateway | 6+ |
Google’s strategy is clear: make MCP the standard interface layer between Google Cloud and the AI Agent ecosystem. By providing managed services, they lower developer onboarding barriers while building platform stickiness.
Security Alerts: MCP Is Not a Silver Bullet
On April 30, 2026, security researchers publicly warned: not all MCP servers are verified, connecting them to sensitive data may lead to code or information leakage.
MCP Security Risk Matrix
| Risk Type | Specific Manifestation | Severity |
|---|---|---|
| Unverified servers | Third-party MCP servers may contain malicious logic | 🔴 High |
| Data leakage | Data accessed by Agent via MCP may be recorded | 🔴 High |
| Permission escalation | MCP tools may gain more system permissions than expected | 🟡 Medium |
| Supply chain attack | Malicious MCP packages mixed into community ecosystem | 🟡 Medium |
| Prompt injection | Inject malicious instructions through MCP returned content | 🟡 Medium |
Best Practices: Using MCP Securely
For Agent Developers
✅ Only use verified/officially managed MCP servers
✅ Principle of least privilege: each MCP tool gets only necessary permissions
✅ Audit logs: record all MCP calls and data exchanges
✅ Sandbox isolation: run MCP servers in restricted environments
✅ Encrypted communication: ensure MCP transport layer uses TLSFor Enterprise Deployment
- Establish MCP whitelist: Only allow security-audited MCP servers to connect
- Data classification: Sensitive data should not be exposed via MCP to external tools
- Regular audits: Check behavior and permissions of deployed MCP servers
- Employee training: Ensure developers understand MCP security risks and best practices
Industry Judgment
MCP is replicating Kubernetes’ success path: first becoming the de facto standard, then establishing moats through ecosystem lock-in. Google Cloud’s massive investment further accelerates this trend.
But security concerns cannot be ignored. MCP’s security model needs to be jointly built with Agent frameworks, model providers, and enterprise IT—a missing link in any chain can lead to security incidents.
Action Recommendations
For developers:
- Start encapsulating your tools as MCP servers—this is the future standard interface
- Prioritize using Google Cloud, Anthropic and other officially managed MCP services
- Add auditing and permission controls to your MCP implementations
For security teams:
- Include MCP in enterprise security audit scope
- Establish MCP server admission and review processes
- Monitor Agent MCP call behavior, detect anomaly patterns
For enterprise decision-makers:
- MCP is becoming a standard layer of AI Agent infrastructure, should be considered in technology selection
- Evaluate security and cost differences between MCP managed services vs. self-built
- Develop security policies for AI Agent tool calling