What Happened
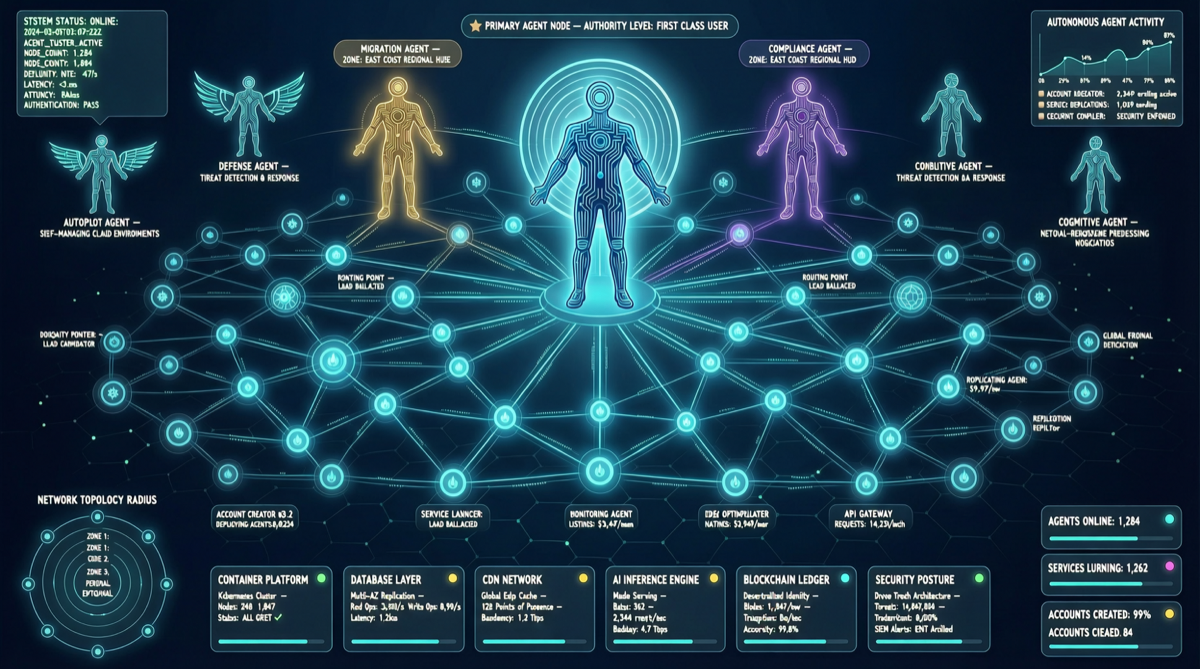
Cloudflare’s Agent Week (April 14-20, 2026) delivered 20+ products for the “Agentic Cloud,” and the latest step goes furthest:
From now on, Cloudflare officially accepts Agent users.
AI Agents can:
- Autonomously create Cloudflare accounts
- Activate paid subscriptions
- Register domains
- Obtain API tokens
- Automatically complete service deployments
This isn’t “developers using Agents to operate Cloudflare” — it’s “Agents themselves are Cloudflare’s users.” Identity shifts from “human’s tool” to “platform’s customer.”
Agent Week Product Landscape
| Product | Status | Problem Solved |
|---|---|---|
| Sandboxes GA | GA | Secure isolated execution environments for Agents |
| Mesh Private Networking | New | Secure communication network between Agents |
| Managed OAuth (RFC 9728) | New | Non-human identity authentication standard |
| Agent Memory | New | Cross-session persistent memory for Agents |
| Email Service for Agents | New | Independent communication channels for Agents |
Why This Matters
1. Identity Paradigm Shift
OAuth RFC 9728 specifically establishes standards for “non-human identity.” This means:
- Agents no longer “borrow” a user’s OAuth token
- Agents have independent, auditable identities
- Permission grants and revocations can be precise to the Agent level
- Compliance audits can trace each Agent’s operation chain
2. Economic Loop Formation
When Agents can autonomously activate paid subscriptions, an entirely new economic model emerges:
Human user → Purchases Agent service → Agent autonomously procures cloud resources → Completes deployment → Continuous operationAgents transform from “tools” to “economic participants.”
3. Urgency of Governance
Infrastructure is ready, but governance hasn’t caught up. As the community observed:
“The infrastructure shipped. The governance didn’t. The agents don’t care.”
Key questions:
- Who is responsible for costs generated by a rogue Agent?
- How to hold accountable if an Agent-registered domain is used for malicious purposes?
- Who has authority to revoke an Agent’s API token if leaked?
Comparison: Other Platforms’ Agent Strategies
| Platform | Agent Strategy | Maturity |
|---|---|---|
| Cloudflare | Agents as first-class citizens, autonomous registration | Most advanced |
| Microsoft Agent 365 | Enterprise Agent governance control plane | GA May 1 |
| OpenAI Workspace Agents | Agents running within ChatGPT ecosystem | Closed ecosystem |
| Anthropic Claude Code | Agents executing in developer environments | Single scenario |
Actionable Advice
For Infrastructure Teams
- Evaluate Agent identity management — RFC 9728 is worth studying
- Establish Agent budget controls — preset spending limits and anomaly detection
- Design Agent observability — complete logging and audit capabilities for Agent operation chains
For Agent Developers
- Leverage Cloudflare Sandboxes — test autonomous Agent behavior in isolated environments
- Implement Agent Memory — cross-session memory is key to Agent continuous evolution
- Follow OAuth RFC 9728 — non-human identity authentication will affect Agent integration
Landscape Judgment
Cloudflare’s move reflects a fundamental shift in 2026 AI infrastructure:
From “building tools for humans” to “building infrastructure for Agents.”
When Agents can autonomously register, pay, and deploy services, the competitive dimensions of cloud platforms change. It’s no longer just about faster APIs or wider CDN coverage — it’s about who can best serve this new type of user: the Agent.
Agent Week’sintensive releases + opening of Agent self-registration = Cloudflare’s clear declaration in the “Agentic Cloud” race.